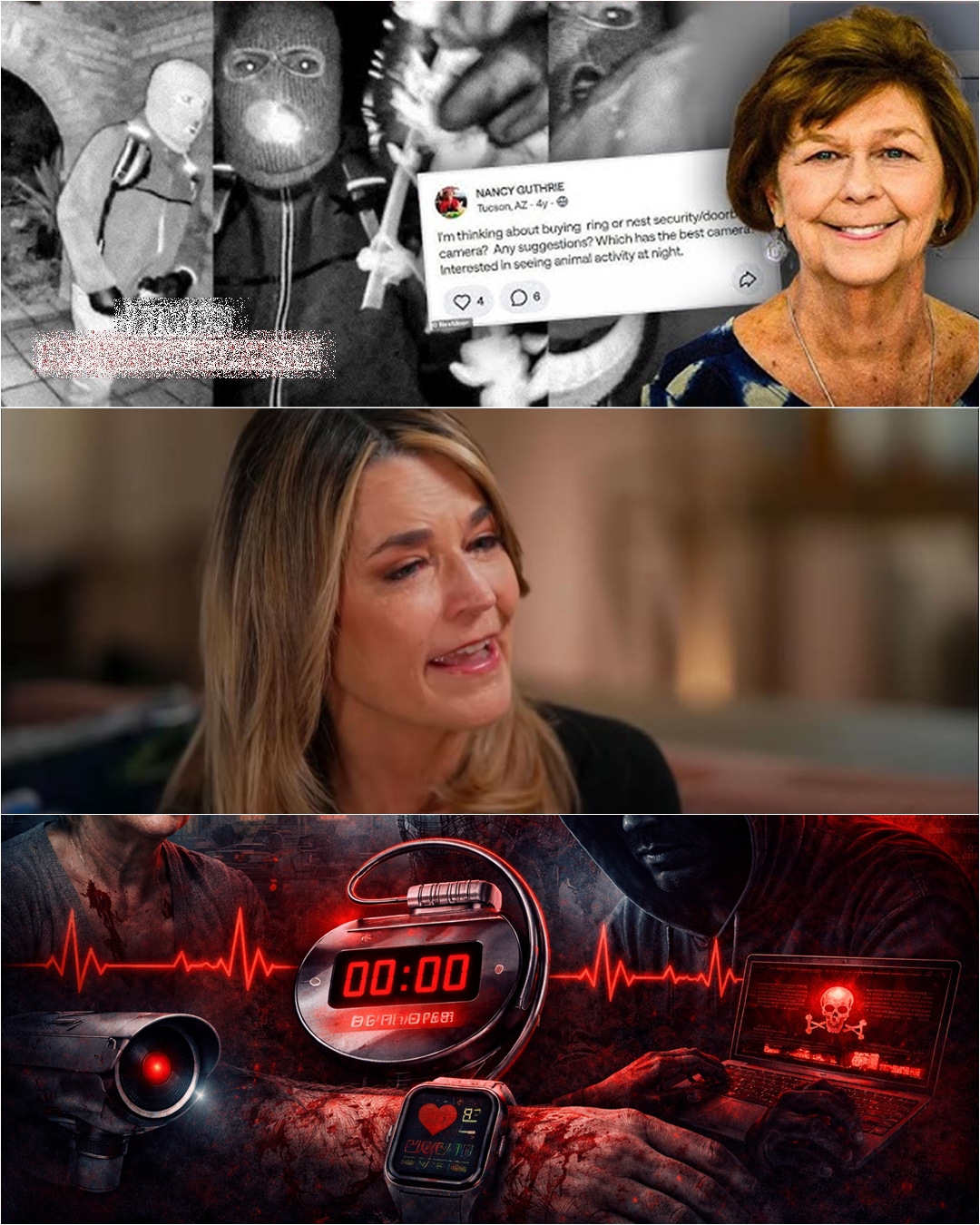
The disappearance of Nancy Guthrie has become a focal point for broader fears about how modern technology intersects with personal safety — particularly for vulnerable populations such as the elderly. Officially, investigators have not confirmed that any medical device, smartwatch, or smart home system was exploited in her case. The known facts remain grounded in a standard missing-person investigation: timeline reconstruction, digital footprint analysis, and witness accounts. However, the case has sparked intense discussion about whether everyday devices could be misused in ways that are not immediately visible.
From a real-world perspective, cybersecurity experts acknowledge that devices like smartwatches and connected health monitors do collect sensitive data — including location, heart rate, and daily routines. If improperly secured, this data could theoretically be accessed or inferred by malicious actors. For elderly users, who may rely more heavily on default settings or assistance from others, the risk is not necessarily in the device itself, but in how it is configured and protected. Weak passwords, shared accounts, and outdated firmware can create openings that are often overlooked.
The idea of a “Trojan horse” — where a system designed for protection becomes a pathway for intrusion — is a recognized concept in cybersecurity. However, turning that into a coordinated physical crime, such as a kidnapping guided by live device data, would require a combination of access, intent, and opportunity that is far more complex than commonly portrayed. Most documented cybercrimes involving consumer devices focus on data theft, surveillance, or financial exploitation, rather than direct physical harm.
What makes the Nancy Guthrie case resonate is not confirmed technological manipulation, but the possibility it raises. In a world where digital and physical boundaries are increasingly blurred, even unverified scenarios can feel plausible. This is why experts emphasize layered security: using strong, unique passwords; enabling two-factor authentication; regularly updating devices; and limiting unnecessary data sharing. These measures significantly reduce exposure, even if they cannot eliminate all risk.
Ultimately, the “lesson” from cases like this is not that technology is inherently dangerous, but that trust without verification can be risky. As investigations continue, the line between fact and fear must remain clear. The true threat may not be a hidden mastermind controlling devices from afar — but the quiet accumulation of small vulnerabilities that, if ignored, could one day be exploited in ways we are only beginning to understand.